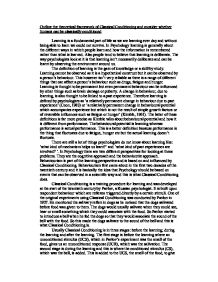
Essay On Technology Invading Privacy - professional essay.
But, technology has a catch 22 concept that includes being at risk for your privacy to be invaded. Just when you think you have something to help protect you and your personal information, the same content can be hacked or tapped into by a knowledgeable person or group of individuals with negative intentions.Technology And Invasion Of Privacy - According to historians, the idea of modern privacy did not exist until the late 19th century. With the creation of cameras that captures snapshots, many people feared that cameras captured and recorded their private lives into physical forms of pictures.INTRODUZIONE In the last twenty years, technology has been changing deeply our society: habits, style of life, and menagement of time are completely different.
Everyone is hearing about invading our privacy by smart phones all over the world, which is our smart phones can reveal our privacy and secrets issues. In the world of technology, everything is possible now. People can track you down wherever you are, it’s completely invasion to our rights as humans.With the ever-increasing profusion of technology, the future of privacy is looking uncertain at best. The internet has thrown a broad net of connection over the entire planet, but as people grow closer, our privacy recedes. The most telling evidence of this was perhaps the global surveillance scandal uncovered by Edward Snowden in 2013.

Technology Is slowly emerging Into critical stages of Invasion and negligence of personal privacy. Web 2. 0 allows people to communicate with each other without speaking one word. The creation of Web 2. Allows social media sites such as Backbone and Twitter possible. “Web 2.